Ransomware is no longer a technical nuisance, it is a board-level risk. The UK Government’s Cyber Security Breaches Survey 2024 reports that 50% of UK businesses identified a cyber security breach or attack in the last 12 months, rising to 70% among medium-sized businesses.
Ransomware remains one of the most disruptive forms of attack, capable of halting operations, exposing sensitive data, and triggering regulatory consequences. For UK SMBs, ransomware protection is no longer optional infrastructure. It is a resilience strategy.
This guide outlines what effective ransomware protection should look like in 2026.
Understanding the Real Risk Landscape
Ransomware attacks have evolved from opportunistic encryption events to sophisticated, multi-stage extortion campaigns.
The National Cyber Security Centre (NCSC) describes ransomware as one of the most significant cyber threats facing UK organisations.
Modern attacks often involve:
- Initial phishing compromise
- Lateral movement across networks
- Data exfiltration
- Encryption of systems
- Double extortion (threat of public data release)
According to IBM’s Cost of a Data Breach Report 2023, the global average cost of a data breach reached $4.45 million.
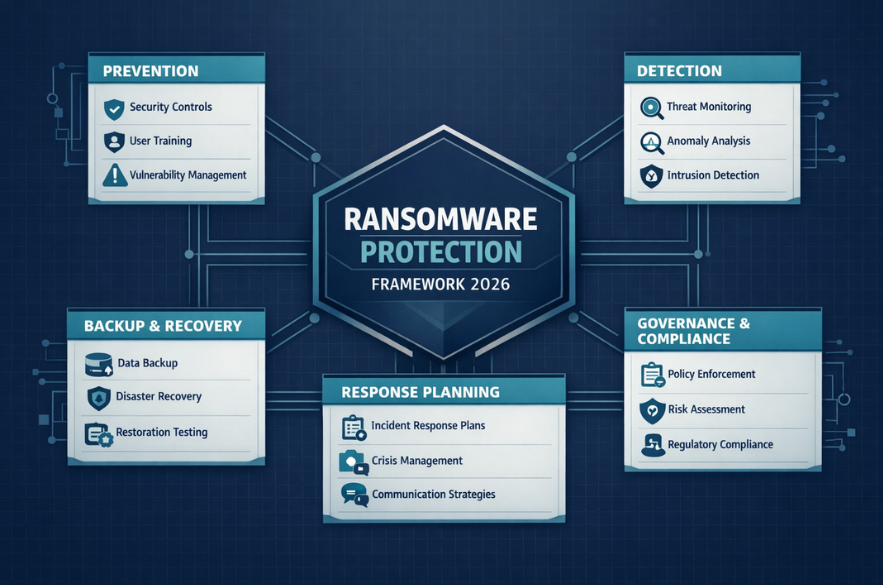
1. Prevention: Reducing Attack Surface
ansomware protection begins long before an attack. The NCSC’s guidance highlights basic cyber hygiene as the most effective defence layer.
Core preventive measures should include:
- Multi-factor authentication (MFA)
- Patch management discipline
- Endpoint detection and response
- Secure configuration of devices
- Email filtering and phishing protection
Microsoft reports that enabling MFA can block over 99.9% of automated account compromise attacks. Prevention is about reducing the probability of initial compromise.

2. Detection: Speed Determines Damage
Even well-protected businesses can be compromised, the difference between containment and catastrophe is often detection speed.
Modern ransomware protection should include:
- Continuous monitoring
- Anomaly detection
- Endpoint behavioural analytics
- Centralised logging
- Security event alerting
Delayed detection increases encryption scope and exfiltration exposure.
3. Backup & Recovery: Your Ultimate Safety Net
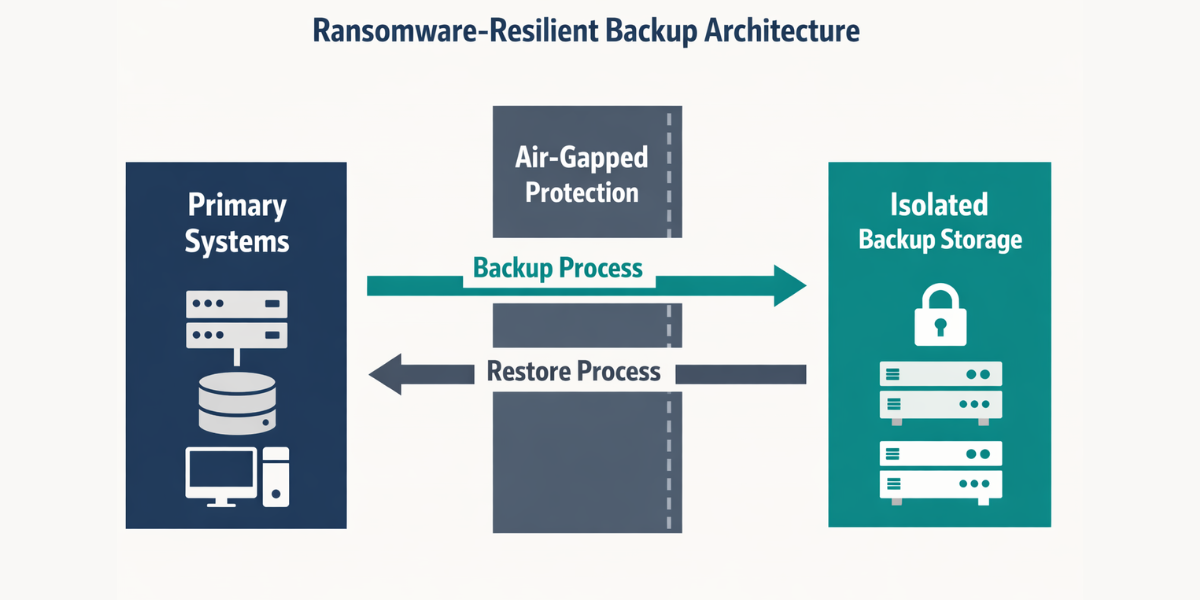
The NCSC is explicit: effective offline backups are critical to ransomware resilience.
However, backups must be:
- Regularly tested
- Isolated from primary networks
- Protected from modification
- Version-controlled
Backups that are accessible from compromised admin accounts often become encrypted alongside production systems.
A recovery strategy should define:
- Maximum acceptable downtime
- Data restoration priorities
- Communication protocols
Ransomware protection without tested recovery is incomplete.
4. Incident Response Planning
When ransomware hits, decision paralysis increases damage, thats why it is recommended having an incident response plan that includes clear escalation procedures and external support contacts.
A ransomware response plan should define:
- Who leads response
- When to involve legal advisors
- Regulatory notification thresholds
- Communication strategy
- Law enforcement engagement
Under UK GDPR, certain breaches must be reported to the ICO within 72 hours.

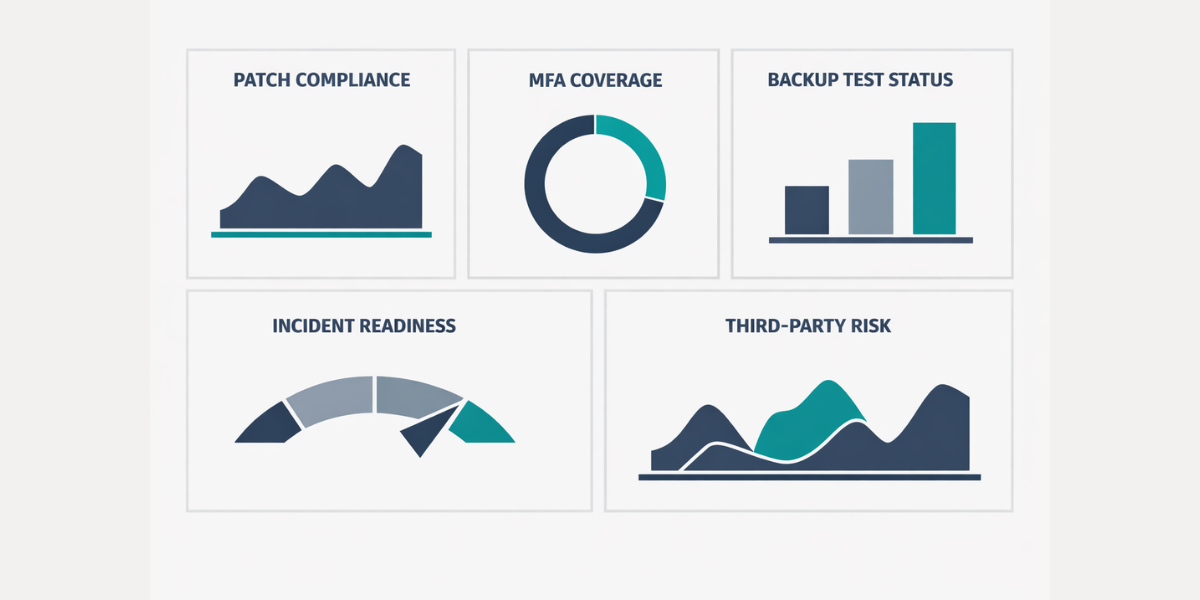
5. Governance & Insurance Expectations
Cyber insurance providers increasingly require demonstrable controls before issuing coverage. The UK Government’s guidance for cyber resilience emphasises board-level accountability for cyber risk. Ransomware protection is therefore a governance responsibility.
Boards should expect reporting on:
- Patch compliance rates
- Backup integrity testing
- MFA coverage
- Incident simulation exercises
- Third-party risk exposure
Security posture is now measurable.
Should You Ever Pay the Ransom?
The NCSC does not recommend paying ransoms, as payment does not guarantee data recovery and may encourage further criminal activity. Paying may also raise regulatory and reputational issues.
The stronger your preparation, the less leverage attackers hold.
The Strategic Reality for UK SMBs
Ransomware protection is not a software purchase. It is a layered resilience framework combining:
- Technical controls
- Governance oversight
- Staff awareness
- Tested recovery
- Regulatory compliance
The Cyber Security Breaches Survey shows that smaller organisations are less likely to implement advanced controls, despite facing similar threat volumes.
If your organisation has antivirus software but no structured ransomware resilience framework, the risk remains unmanaged.
I-Net Software Solutions provides a ransomware protection and cyber resilience review tailored to UK SMBs. We assess prevention controls, detection capability, backup integrity, governance maturity, and regulatory exposure.
The objective is not fear-based selling, it is operational continuity.
FAQs
Recommended Read
- The Complete Guide to Ransomware Protection for UK Businesses (2026)
- What Should UK SMBs Expect from UI UX Design Services in 2026?
- A Practical Data Governance Framework for SMBs

- Why Passing Cybersecurity Compliance Doesn’t Mean You’re Secure

- Why Consistency Beats Creativity in Scalable UX

- Turning Everyday Business Data Into AI-Ready Assets
